Linux网络扫描和嗅探工具—Nmap
1、简介
Nmap,也就是Network Mapper,是Linux下的网络扫描和嗅探工具包。它由Fyodor编写并维护。由于Nmap品质卓越,使用灵活,它已经是渗透测试人员必备的工具。
其基本功能有三个:
是扫描主机端口,嗅探所提供的网络服务
是探测一组主机是否在线
还可以推断主机所用的操作系统,到达主机经过的路由,系统已开放端口的软件版本
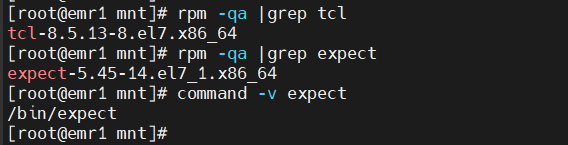
2、安装
[root@******.stie ~]# yum install nmap
3、Nmap命令常用格式
[root@******.stie ~]# man nmap -sS: TCP SYN 扫描 (又称半开放,或隐身扫描) -P0: 允许你关闭 ICMP pings. -sV: 打开系统版本检测 -O: 尝试识别远程操作系统 -A: 同时打开操作系统指纹和版本检测 -v: 详细输出扫描情况.
4、扫描出其对外开放的服务
[root@******.stie ~]# nmap 172.17.120.11 Starting Nmap 6.40 ( http://nmap.org ) at 2020-03-2621:35 CST Nmap scan report forelasticsearch-01.crawler-beta (172.17.120.11) Host is up (0.00019s latency). Not shown: 998closed ports PORT STATE SERVICE 22/tcp open ssh 80/tcp open http MAC Address: 02:00:1F:B5:00:6B (Unknown) Nmap done: 1IP address (1 host up) scanned in11.16 seconds # 可以看出只开放了22端口和80端口
5、nmap -p 端口 IP(域名),判断ip是否开放指定端口
[root@******.stie ~]# nmap -p 80 172.17.120.11 Starting Nmap 6.40 ( http://nmap.org ) at 2020-03-2621:37 CST Nmap scan report forelasticsearch-01.crawler-beta (172.17.120.11) Host is up (0.00037s latency). PORT STATE SERVICE 80/tcp open http MAC Address: 02:00:1F:B5:00:6B (Unknown) Nmap done: 1IP address (1 host up) scanned in11.09 seconds ---------------------------------------------------------------------------------------- [root@******.stie ~]# nmap -p 8080 172.17.120.11 Starting Nmap 6.40 ( http://nmap.org ) at 2020-03-2621:38 CST Nmap scan report forelasticsearch-01.crawler-beta (172.17.120.11) Host is up (0.00039s latency). PORT STATE SERVICE 8080/tcp closed http-proxy MAC Address: 02:00:1F:B5:00:6B (Unknown) Nmap done: 1IP address (1 host up) scanned in11.10 seconds # 可以看出80端口开放,8080端口没有开放
6、在网络寻找所有在线主机
[root@******.stie ~]# nmap -sP 172.17.120.* [root@******.stie ~]# nmap -sP 172.17.120.0/24
7、增加端口和网段
[root@******.stie ~]# nmap -p 443,22,80 172.17.120.11 [root@******.stie ~]# nmap -p 443,22,80 172.17.120.11-14
8、扫描地址段是排除某个IP地址
[root@******.stie ~]# nmap 172.17.120.11-14 --exclude 172.17.120.13
9、扫描多个地址时排除文件里的IP地址
[root@******.stie ~]# cat ex.txt 172.17.120.11 172.17.120.14 [root@******.stie ~]# nmap 172.17.120.11-14 --excludefile ex.txt
10、在某段子网上查找未占用的 IP
[root@******.stie ~]# nmap -T4 -sP 172.17.120.0/24 && egrep “00:00:00:00:00:00″ /proc/net/arp
11、服务版本识别(-sV),Nmap可以在进行端口扫描的时候检测服务端软件的版本信息
[root@******.stie ~]# nmap -sV 172.17.120.11 -p 80 Starting Nmap 6.40 ( http://nmap.org ) at 2020-03-2621:42 CST Nmap scan report forelasticsearch-01.crawler-beta (172.17.120.11) Host is up (0.00041s latency). PORT STATE SERVICE VERSION 80/tcp open http nginx 1.16.1 MAC Address: 02:00:1F:B5:00:6B (Unknown) Service detection performed. Please report any incorrect results at http://nmap.org/submit/ . Nmap done: 1IP address (1 host up) scanned in17.21 seconds
12、操作系统检测(-O),Nmap还能识别目标主机的操作系统
[root@******.stie ~]# nmap -O 172.17.120.11 Starting Nmap 6.40 ( http://nmap.org ) at 2020-03-2621:44 CST Nmap scan report forelasticsearch-01.crawler-beta (172.17.120.11) Host is up (0.00037s latency). Not shown: 998closed ports PORT STATE SERVICE 22/tcp open ssh 80/tcp open http MAC Address: 02:00:1F:B5:00:6B (Unknown) No exact OS matches forhost (If you know what OS is running on it, see http://nmap.org/submit/ ). TCP/IP fingerprint: OS:SCAN(V=6.40%E=4%D=3/26%OT=22%CT=1%CU=34467%PV=Y%DS=1%DC=D%G=Y%M=02001F%T OS:M=5E7CB1E6%P=x86_64-redhat-linux-gnu)SEQ(SP=107%GCD=1%ISR=10C%TI=Z%TS=U) OS:SEQ(SP=107%GCD=1%ISR=10C%TI=Z%II=I%TS=U)OPS(O1=M5B4NNSNW9%O2=M5B4NNSNW9% OS:O3=M5B4NW9%O4=M5B4NNSNW9%O5=M5B4NNSNW9%O6=M5B4NNS)WIN(W1=7210%W2=7210%W3 OS:=7210%W4=7210%W5=7210%W6=7210)ECN(R=Y%DF=Y%T=40%W=7210%O=M5B4NNSNW9%CC=Y OS:%Q=)T1(R=Y%DF=Y%T=40%S=O%A=S+%F=AS%RD=0%Q=)T2(R=N)T3(R=N)T4(R=Y%DF=Y%T=4 OS:0%W=0%S=A%A=Z%F=R%O=%RD=0%Q=)T5(R=Y%DF=Y%T=40%W=0%S=Z%A=S+%F=AR%O=%RD=0% OS:Q=)T6(R=Y%DF=Y%T=40%W=0%S=A%A=Z%F=R%O=%RD=0%Q=)T7(R=Y%DF=Y%T=40%W=0%S=Z% OS:A=S+%F=AR%O=%RD=0%Q=)U1(R=Y%DF=N%T=40%IPL=164%UN=0%RIPL=G%RID=G%RIPCK=G% OS:RUCK=G%RUD=G)IE(R=Y%DFI=N%T=40%CD=S) Network Distance: 1hop OS detection performed. Please report any incorrect results at http://nmap.org/submit/ . Nmap done: 1IP address (1 host up) scanned in22.89 seconds
13、找到目标主机开放了哪些 UDP端口。为提高扫描速度,我们仅扫描 53端口 (DNS)和161端口(SNMP)
[root@******.stie ~]# nmap -sU 172.17.120.11 -p 53,161 Starting Nmap 6.40 ( http://nmap.org ) at 2020-03-2622:01 CST Nmap scan report forelasticsearch-01.crawler-beta (172.17.120.11) Host is up (0.00044s latency). PORT STATE SERVICE 53/udp closed domain 161/udp closed snmp MAC Address: 02:00:1F:B5:00:6B (Unknown) Nmap done: 1IP address (1 host up) scanned in11.09 seconds
14、启用Nmap的-6选项即可扫描IPv6的目标主机
[root@******.stie ~]# nmap -6fe80::a00:27ff:fe43:1518
15、在局域网上扫找 Conficker 蠕虫病毒
[root@******.stie ~]# nmap -PN -T4 -p139,445 -n -v –script=smb-check-vulns –script-args safe=1 172.17.120.1-254
16、扫描网络上的恶意接入点 (rogue APs)
[root@******.stie ~]# nmap -A -p1-85,113,443,8080-8100 -T4 –min-hostgroup 50 –max-rtt-timeout 2000 –initial-rtt timeout 300 –max-retries 3 –host-timeout 20m –max-scan-delay 1000 -oA wapscan 172.17.120.0/24
17、使用诱饵扫描方法来扫描主机端口
[root@******.stie ~]# nmap -sS 172.17.120.12 -D 172.17.120.20
18、显示网络上共有多少台 Linux 及 Win 设备
[root@******.stie ~]# nmap -F -O 172.17.120.0-255 | grep “Running: ” > /tmp/os; echo “$(cat /tmp/os | grep Linux \| wc -l) Linux device(s)”; echo “$(cat /tmp/os | grep Windows | wc -l) Window(s) device”